Compromised Card Monitoring
Proactively find and cancel stolen credit and debit cards before they can be used for fraud.

Overview
Protect your institution and customers from the financial losses that follow massive retailer card breaches. Compromised Card Monitoring notifies banks when cards are found for sale on the black market, so that they can be cancelled before any fraud occurs.
Boost Breach Response
Banks can’t stop breaches on retailer infrastructure, but Compromised Card Monitoring provides a big head start in stopping the fraud losses they cause.
Immediately Start Finding Stolen Cards
Since Compromised Card Monitoring is cloud-based, it’s easy to install and can detect cards instantly upon implementation.
Increased Visibility into Security Gaps
Card fraud continues evolving to evade legacy protection methods. Find and plug vulnerabilities before cybercriminals find them.
An Innovative Way to Limit Card Fraud
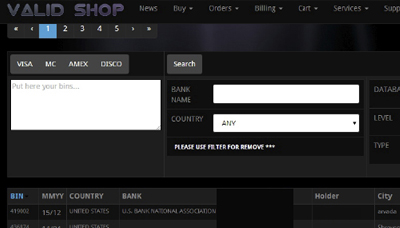
Compromised Card Monitoring scours black markets for stolen credentials and cards, warning banks and allowing them to take action before any fraud happens. This cutting-edge approach to mitigating card cloning and account takeover is unique in the fraud prevention industry.

Reduce the Financial and Reputational Losses from Major Breaches
Save the millions of dollars that banks typically spend on card replacements, court costs, and lost business following a massive retail breach. Locate the specific cards that have been compromised, protect customers and preserve your institution’s reliable reputation.
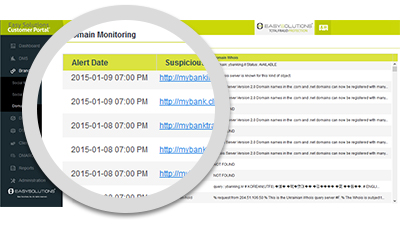
Full Notifications and Reporting
Every time our agents detect one of your institution’s cards for sale on the black market, a notification is immediately sent through the Easy Solutions Customer Portal. These notifications can also be compiled into thorough, downloadable reports in the portal for easy reference.

Part of a Complete Fraud Intelligence Solution
Compromised Card Monitoring is a part of Detect Monitoring Service, a solution that stops a wide range of fraud attacks in real time and totally removes them from the Internet. With an industry-leading average attack takedown time of 3.6 hours, DMS is the most effective and proactive threat detection and removal service available today.


